Information-stealing backdoor by new malware: a new type is targeting Discord users, modifying the Windows Discord client so that it is transformed into a backdoor and an information-stealing Trojan.
Summary
The Windows Discord client is an Electron application, which means that almost all of its functionality is derived from HTML, CSS and JavaScript. "This allows the malware to modify its core files so that the client performs malicious behavior at startup."
Discovered by the researcher Malware Hunter Team earlier this month, malware - backdoor is called "Spidey Bot.", based on the name of the Discord command and control channel with which the 'malware' communicated. Interestingly, see the article below for a comment which, however, states that its real name is "BlueFace".
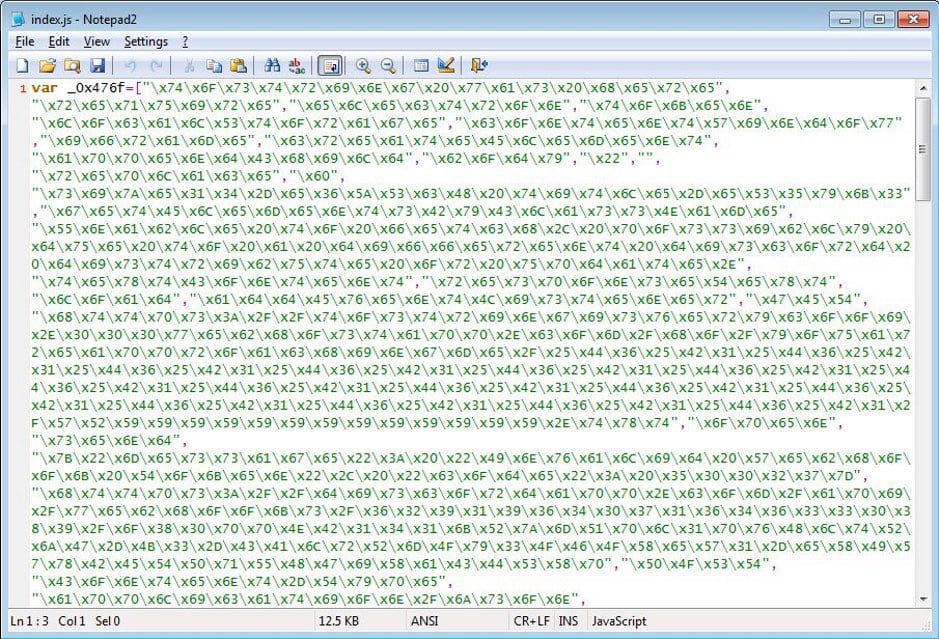
Malicious JavaScript
When installed, the malware adds its own malicious JavaScript to the files% AppData% \ Discord \ [version] \ modules \ discord_modules \ index.js and % AppData% \ Discord \ [version] \ modules \ discord_desktop_core \ index.js .
The backdoor malware will shut down and restart the Discord application so that the new JavaScript changes can be executed.
Once started, JavaScript will execute various Discord API commands and JavaScript functions to collect a variety of information about the user that will be sent via a Discord webhook to the attacker.
New malware: information collected
The information collected and sent to the attacker includes:
- Disagree user token
- Victim's time zone
- Screen resolution
- Victim's local IP address
- Victim's public IP address via WebRTC
- User information such as username, email address, phone number and more
- If they have stored payment information
- Zoom factor
- Browser user agent
- Discord version
- The first 50 characters of the Windows clipboard victims
The content of the clipboard is especially worrying, as it can allow the user to steal passwords, personal information or other confidential data that has been copied by the user.
The Gightdio Function
The Gightdio function that acts as a backdoor in the new malware
Once the information has been sent, the Discord malware will execute the fightdio () function, which acts as a backdoor.
This function will connect to a remote site to receive an extra command to execute. This allows the attacker to carry out other malicious activities, such as stealing payment information, if any, executing commands on the computer or potentially installing other malware.
At the moment, the site above is down, but it's not known whether a different sample uses a different site or not. In addition, a commenter below claims that the malware has been discontinued, but we have no way of confirming this.
Discord messages
Researcher and reverse engineer Vitali Kremez, who also analyzed the malware, told BleepingComputer that the infection was seen using file names such as "Blueface Reward Claimer.exe" and "Synapse X.exe". Although he is not 100% sure how it is being spread, Kremez feels that the attacker is using Discord messages to spread the malware.
As this infection shows no external indication that it has been compromised, a user has no idea that they are infected unless they run a network detection and see the unusual API and web hook calls.
If the installer is detected and removed, the modified Discord files will still remain infected and will continue to run every time you start the client. The only way to clean up the infection will be to uninstall the Discord application and reinstall it so that the modified files are removed.
Worse still, after more than two weeks, this Discord malware still has only 24/65 detections on VirusTotal.
How to check if you are infected by the new Malware
Checking whether your Discord client has been modified is very easy, since the target files usually have just one line of code.
To check the % AppData% \ Discord \ [version] \ modules \ discord_modules \ index.js, simply open it in Notepad and it should only contain the single line of "module.exports = require ('./ discord_modules.node'); " as shown below.
For the file % AppData% \ Discord \ [version] \ modules \ discord_desktop_core \ index.js , it should only contain the "module.exports = require ('./ core.asar');" as shown below.
If one of the two files contains code other than that shown above, uninstall and reinstall the Discord client and confirm that the modifications have been removed.
It's important to remember, however, that other malware can easily modify other JavaScript files used by the Discord client, so these instructions are only for that specific malware.
How Discord can protect
How Discord can protect you from malware threats
After publishing this article, we received many questions about how Discord can alert users to changes in the client.
Discord can do this by creating a hash for each client file when a new version is released. After installation, if the file is modified, this hash will be changed.
When the Discord client is started, it can perform a file integrity check and verify that the hashes of the current file match the Discord client's default hashes. If they are different, that file has been modified and the application can display a warning, like the mock-up we've created below, which allows the user to continue loading the client or cancel it.
This check should be done using native code rather than another JavaScript file, which can be easily modified.
Update 10/24/19: Added sections on checking if specified JS files have been modified and how Discord can monitor these types of modifications.
Update 10/24/19 5:25PM EST: Added information about the C2 being dead, that the real name for this infection may be BlueFace, and that the malware is said to be discontinued.
Source: //www.bleepingcomputer.com