
5 Crucial Points About Cloud Backup and Recovery for Your Business
Backup refers to the process of making copies of data or data files for use in the event of the loss or destruction of the original data or files.

Backup refers to the process of making copies of data or data files for use in the event of the loss or destruction of the original data or files.

With effective hardware asset management, you can make huge savings on hardware and software ... check out our valuable tips on ...

Tips on how to avoid ransomware attacks... prevent your data from being kidnapped for ransom?

Step by step to activate and register licenses on the FortiGate firewall from Fortinet.

This article provides a detailed guide to TI security with the Fortinet Firewall. It covers everything from configuration to best practices for maximizing the protection of your network. Ideal for TI professionals looking to improve their information security skills.
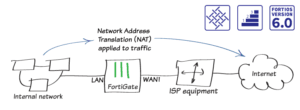
Installing a FortiGate in NAT mode... ortiGate in NAT mode, to securely connect a private network to the Internet

Growing demand for cyber security... Take advantage of networking opportunities.

Endpoint security; this term is one of the most heard in recent years during major security events, conferences, webinars and blogs. Some call it a mandatory part of the security platform, others say it's just a new term for antivirus and others call it an overrated approach. One thing is clear: it's a term that doesn't immediately clarify what you can expect from it.

Several malicious spam campaigns were detected simultaneously, delivering malware - including ransomware, banking Trojans and backdoors - to victims in different geographical regions
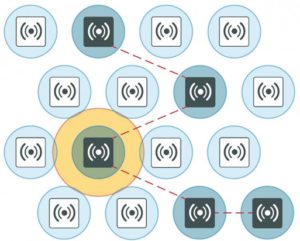
7 foolproof tips for configuring your FortiAP. Definitive guide to configuring the Fortinet FortiAP Access Point